UAE Cyber Security Council Flags Human Error as Primary Cyber Risk
Everyday lapses — not technical gaps — continue to be the biggest drivers of sensitive data exposure, a Cyber Pulse advisory finds.
News
- World’s First AI-Designed Vaccine Targets Future Pandemics
- Dubai’s ‘SME in a Box’ Reimagines Business Setup as an Integrated Service
- AI Dispatch | The Rise of the Agent-First World
- OpenAI, Anthropic & Microsoft CEOs Call for Stricter Laws Against AI Biothreats
- Sharjah Moves to Operationalize Agentic AI Across Government Functions
- UAE Expands AI Push With New Leadership Development Program
[Image source: Krishna Prasad/MITSMR Middle East]
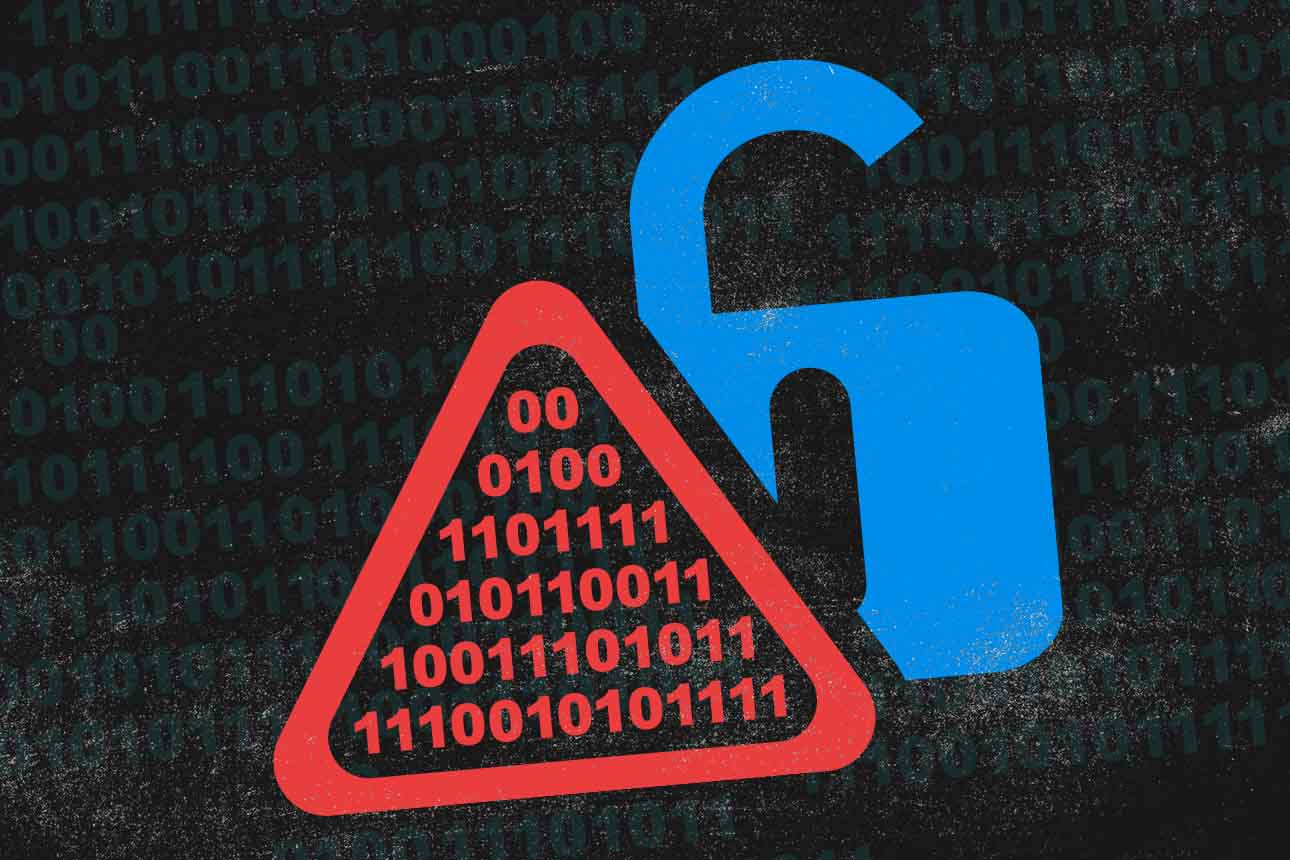
The UAE Cyber Security Council has sharpened its focus on a familiar but persistently under-addressed problem: the gap between available security tools and everyday user behavior.
While organizations continue to invest in cloud infrastructure and digital collaboration tools, the Council, in its latest bulletin of the “Cyber Pulse” campaign, points to evidence that basic lapses — such as poorly managed access permissions — remain a primary source of vulnerability.
It cites data suggesting that 68% to 77% of privately shared files may still be accessible to unintended users, highlighting the limits of default privacy settings and the illusion of control in cloud environments.
Encryption, in this context, is positioned less as an advanced safeguard and more as a baseline requirement. The Council stresses that cloud storage does not inherently secure data, particularly when files are transmitted or shared across networks. Without encryption, sensitive information remains exposed to interception or unauthorized access, even within ostensibly protected systems.
The guidance itself is not novel: strong, frequently updated passwords, two-factor authentication, restricted sharing links, and routine audits of privacy settings. But the emphasis lies in consistency rather than innovation.
Additional measures such as securing Wi-Fi networks, maintaining updated software, limiting app permissions, and using VPNs on public networks reflect a layered defense model that depends heavily on user compliance.
Notably, the Council also highlights data hygiene as a security practice. Deleting unused files and links, along with regular backups and disciplined database management, are framed as critical steps in reducing the attack surface.
Now in its second year, the “Cyber Pulse” campaign signals a broader shift: from infrastructure-led cybersecurity to user-centric risk mitigation. The message is clear: as digital systems become more distributed and cloud-dependent, the weakest link is less likely to be the technology itself and more likely to be the everyday decisions made by its users.